If you’ve ever enabled Hyper-V on a BitLocker-protected Windows machine, you might have been greeted with an unwelcome surprise: BitLocker suddenly asking for your recovery key on every reboot.
This is a common frustration for developers, IT pros, and security-conscious users. The good news is that it’s not a bug — it’s how BitLocker is designed. The better news? You can configure your system so that Hyper-V and BitLocker coexist peacefully.
Why Hyper-V Triggers BitLocker Recovery
BitLocker protects your system by measuring parts of the boot process against known “good” values, which it stores in the TPM (Trusted Platform Module).
When you enable Hyper-V, Windows makes changes to the boot configuration and hypervisor. To BitLocker, that looks like someone tampered with your system. Since BitLocker is cautious by design, it demands the recovery key before proceeding.
Common scenarios where this happens:
- Turning Hyper-V on or off in Windows Features.
- Running virtualization-based security (VBS), Credential Guard, or Device Guard.
- Changing Secure Boot or virtualization settings in BIOS/UEFI.
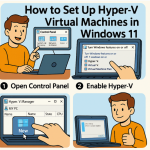
How to Set Up Hyper-V and BitLocker the Right Way
1. Suspend BitLocker Before Enabling Hyper-V
BitLocker needs to “learn” that Hyper-V is part of your system’s normal state. To do that, suspend it first:
manage-bde -protectors -disable C:
- Enable Hyper-V through Windows Features or PowerShell.
- Reboot into the Hyper-V-enabled environment.
- Re-enable BitLocker protection:
manage-bde -protectors -enable C:
From now on, Hyper-V will be part of the expected boot environment.
2. Keep Hyper-V Either Always On or Always Off
The most common cause of repeated recovery prompts is toggling Hyper-V on and off. Each time, BitLocker sees a different environment.
- If you use Hyper-V regularly, leave it on.
- If you don’t need it often, consider disabling it permanently and using alternatives like WSL2 with Virtual Machine Platform (which doesn’t require the full Hyper-V hypervisor).
3. Adjust PCR Bindings (Advanced Option)
BitLocker uses PCRs (Platform Configuration Registers) in the TPM to measure system integrity. By default, PCR 11 includes the hypervisor state.
If you want to prevent Hyper-V changes from triggering recovery prompts, you can exclude PCR 11:
manage-bde -protectors -delete C: -type TPM
manage-bde -protectors -add C: -tpm -PCRList 0,2,4
⚠️ This slightly reduces security, since hypervisor changes won’t be detected. It’s fine for dev/test environments, but enterprises may prefer the stricter default.
4. Store Your Recovery Key Safely
No matter how well you configure things, you should always keep your BitLocker recovery key handy. Save it to:
- Your Microsoft account (aka.ms/recoverykey)
- A USB drive
- Azure AD or Active Directory (for managed devices)
That way, you’ll never be locked out.
5. A Tip for WSL2 Users
If your only reason for enabling Hyper-V is Windows Subsystem for Linux 2, you may not need the full Hyper-V role. WSL2 can run with just the Virtual Machine Platform feature enabled, which avoids frequent BitLocker prompts.
The Smooth Path: One-Time Setup
For most users, the easiest and safest workflow is:
- Suspend BitLocker.
- Enable Hyper-V.
- Reboot.
- Resume BitLocker.
- Keep Hyper-V enabled permanently.
This way, BitLocker’s TPM baseline always matches your boot environment, and you won’t see recovery prompts every time you restart.
Hyper-V and BitLocker don’t have to be enemies. The recovery prompts you see aren’t glitches — they’re signs that BitLocker is doing its job. With a little setup, you can have the best of both worlds: secure full-disk encryption and powerful virtualization.