In today’s digital-first world, managing user identities and access securely is paramount. Microsoft Azure provides a robust platform for identity management through Azure Active Directory (Azure AD), helping organizations protect sensitive data while ensuring seamless user experiences. Understanding the differences between authentication and authorization in Azure, and how Azure AD facilitates them, is crucial for IT professionals, developers, and security experts alike.
In this article, we will explore the fundamentals of identity in Azure, the role of Azure AD, and how authentication and authorization work together to secure cloud applications and resources.
What is Azure Active Directory?
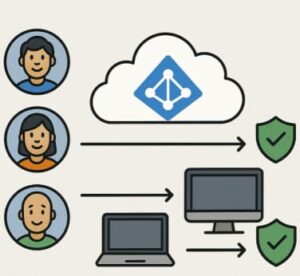
Azure Active Directory (Azure AD) is Microsoft’s cloud-based identity and access management (IAM) service. Unlike the traditional on-premises Active Directory (AD), which focuses on managing Windows-based devices and users, Azure AD extends identity management to cloud services, SaaS applications, and mobile devices.
Azure AD enables organizations to:
- Manage user identities centrally
- Enable single sign-on (SSO) for thousands of applications
- Control access to resources based on policies and roles
- Implement multi-factor authentication (MFA) to strengthen security
- Integrate with on-premises directories for hybrid identity management
With Azure AD, IT teams can reduce the risks associated with stolen credentials, manage external collaborators securely, and simplify the user experience.
Authentication vs. Authorization in Azure
Identity management often involves two closely related concepts: authentication and authorization. While these terms are sometimes used interchangeably, they serve different purposes in securing access.
Authentication
Authentication is the process of verifying a user’s identity. When a user attempts to sign in to an application or service, Azure AD checks their credentials—such as a username and password, a security token, or a biometric factor. If the credentials are valid, the user is authenticated and granted access to the system.
Azure AD supports multiple authentication methods:
- Password-based authentication: Standard username and password login
- Multi-factor authentication (MFA): Adds an extra layer of security with SMS, email, or app-based verification
- Passwordless authentication: Uses biometrics, security keys, or device-based authentication to eliminate passwords
- Federated authentication: Integrates with other identity providers using protocols like SAML or OpenID Connect
Authorization
Once a user is authenticated, authorization determines what resources or actions they are allowed to access. This involves checking the user’s roles, groups, and assigned permissions. In Azure, authorization can be managed using Role-Based Access Control (RBAC), which enables granular access management for Azure resources.
Key points about authorization in Azure:
- Users are assigned roles such as Owner, Contributor, or Reader
- Access can be controlled at subscription, resource group, or individual resource levels
- Conditional Access policies can enforce access requirements based on location, device, or risk level
In essence, authentication answers the question, “Who are you?” while authorization answers, “What are you allowed to do?”
How Azure AD Secures Applications
Azure AD not only secures access to Microsoft services like Microsoft 365 but also third-party SaaS applications and custom enterprise apps. Here are some key features:
- Single Sign-On (SSO)
SSO allows users to log in once and access multiple applications without repeated prompts for credentials. Azure AD supports SSO for thousands of popular applications, improving productivity while reducing password fatigue. - Conditional Access
Conditional Access policies enforce intelligent access control based on conditions such as user location, device compliance, or risk detection. For example, access may be blocked if a user attempts to log in from an untrusted network. - Privileged Identity Management (PIM)
PIM helps organizations manage, control, and monitor privileged accounts. Temporary elevated access can be granted to administrators, reducing the risk of misuse. - Identity Protection
Azure AD Identity Protection uses machine learning to detect suspicious login activities, such as impossible travel or unfamiliar sign-in locations, and automatically prompts for verification or blocks risky logins.
Integrating Azure AD with Applications
Organizations can integrate Azure AD with their applications using standard protocols like OAuth 2.0, OpenID Connect, and SAML. This allows seamless authentication and authorization flows between users and applications.
- OAuth 2.0: Enables secure delegated access, allowing applications to access resources on behalf of the user without sharing credentials.
- OpenID Connect: Built on OAuth 2.0, OpenID Connect adds identity verification, providing authentication in addition to authorization.
- SAML (Security Assertion Markup Language): Enables SSO for enterprise applications, allowing the user to log in once and access multiple services.
By leveraging these protocols, developers can ensure their applications comply with modern security standards while providing a smooth user experience.
Best Practices for Azure Identity Management
To maximize security and efficiency, organizations should follow these best practices:
- Enable Multi-Factor Authentication (MFA) for all users, especially for privileged accounts.
- Use Conditional Access policies to enforce access controls based on risk factors.
- Implement Role-Based Access Control (RBAC) to assign least privilege access.
- Monitor user activities and sign-in logs to detect suspicious behavior.
- Adopt passwordless authentication methods to reduce reliance on passwords.
- Regularly review external and guest accounts to maintain secure collaboration.
Implementing these practices ensures that Azure AD not only authenticates users but also effectively protects resources from unauthorized access.
Managing identities in the cloud is a critical component of modern cybersecurity strategies. Azure Active Directory provides a comprehensive platform for authentication and authorization, enabling organizations to protect sensitive information, simplify user access, and meet compliance requirements.
By understanding the differences between authentication and authorization, integrating Azure AD with applications, and following best practices, IT teams can create a secure, scalable, and efficient identity management framework.
Investing in robust identity solutions like Azure AD is no longer optional—it’s essential for any organization navigating today’s complex digital landscape.