As organizations increasingly rely on Microsoft 365 for productivity and collaboration, securing your tenant has never been more critical. Weak configurations or overlooked settings can leave your environment vulnerable to breaches, data leaks, and compliance violations. Here’s a practical guide for Microsoft 365 administrators to identify and mitigate common security pitfalls.
🚨 Common Weak Points in Microsoft 365 Tenants
1. Default Security Settings Aren’t Enough
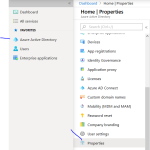
While Entra Security Defaults offer a baseline, they don’t cover advanced scenarios. Without custom conditional access policies or device compliance rules, attackers can exploit gaps in identity protection
2. Trial Tenants Are a Target
Trial tenants, especially those used in MVP or developer programs, are often exploited for spam or phishing. Microsoft has restricted external communications from such tenants unless they meet compliance standards
3. Identity Infrastructure Exploits
Misconfigured hybrid identity setups or weak MFA enforcement are prime targets for attackers. These vulnerabilities often serve as entry points for lateral movement and privilege escalation
4. Browser Session Residue
Cached sessions in browsers can expose sensitive tenant data when switching between accounts. Always use private browsing or clear sessions when managing multiple tenants
🛡️ Best Practices to Strengthen Your Tenant
✅ Enforce Multi-Factor Authentication (MFA)
Apply MFA to all users, especially admins. Go beyond defaults—use conditional access to enforce location, device, and risk-based policies.
✅ Disable Legacy Authentication
Legacy protocols like POP and IMAP don’t support MFA and are often exploited. Disable them unless absolutely necessary.
✅ Monitor with Microsoft Sentinel or SIEM
Integrate your tenant with Microsoft Sentinel or another SIEM to centralize threat detection and automate response workflows
✅ Enable Audit Logging
Ensure audit logs are enabled and retained for at least 90 days. Use them to track user activity, admin changes, and potential breaches.
✅ Regularly Test Network Connectivity
Use Microsoft’s connectivity tools to test your network’s path to Microsoft 365. Poor routing can expose your tenant to man-in-the-middle attacks
✅ Review Admin Roles and Access
Apply the principle of least privilege. Use role-based access control (RBAC) and regularly audit who has admin rights.
📚 Additional Resources
- https://dellenny.com/microsoft-365-purview-your-unified-shield-for-data-governance-compliance/
- https://dellenny.com/microsoft-365-defender-a-unified-shield-for-it-pros-and-end-users/
- https://dellenny.com/protecting-your-data-a-guide-to-microsoft-365-backup-solutions/
- https://dellenny.com/microsoft-defender-for-365-your-all-in-one-security-shield-for-modern-threats/