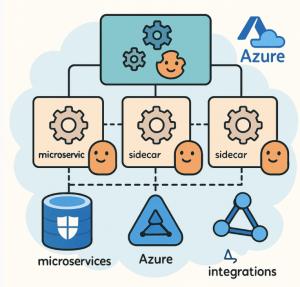
As organizations modernize applications using microservices and cloud-native architectures, managing how these services communicate becomes increasingly complex. Microservices often run across distributed environments, scaling dynamically, and interacting over the network. This is where the Service Mesh architecture pattern comes in — providing a dedicated infrastructure layer for service-to-service communication, security, and observability.
In the Azure ecosystem, implementing a Service Mesh can simplify operational challenges while improving reliability and control of microservices deployments.
What is a Service Mesh?
A Service Mesh is an infrastructure layer that transparently manages communication between microservices. Instead of embedding networking, security, and observability logic within the application code, a service mesh offloads these responsibilities to a dedicated layer, usually implemented using sidecar proxies running alongside each service instance.
This design allows developers to focus on business logic, while the service mesh handles:
- Traffic routing and resiliency (load balancing, retries, failover)
- Security (mTLS for encryption, authentication, authorization)
- Observability (metrics, logs, traces for monitoring service health)
Service Mesh in Azure
Azure provides multiple options to implement a service mesh, most commonly through:
- Azure Kubernetes Service (AKS) with service mesh add-ons like Linkerd, Istio, or Consul.
- Open Service Mesh (OSM) – a lightweight, CNCF project that is natively integrated into Azure.
Why use a Service Mesh on Azure?
- Seamless integration with Azure Active Directory for service identity.
- Native support for Azure Monitor and Application Insights for observability.
- Scalability and resilience in distributed environments managed through AKS.
Key Capabilities of Service Mesh Architecture in Azure
1. Service-to-Service Communication
In microservices environments, services often need to communicate reliably under fluctuating load. A service mesh provides:
- Dynamic service discovery – no hardcoded endpoints.
- Smart traffic routing – supports canary deployments, blue/green deployments, and traffic splitting.
- Resiliency – automatic retries, circuit breakers, and timeouts.
Example in Azure:
With Istio on AKS, you can route 10% of traffic to a new version of a service for testing before scaling it up to 100%.
2. Security
Security in microservices must be zero-trust by design. A service mesh enforces secure communication without requiring developers to implement it manually.
- Mutual TLS (mTLS) – all service-to-service traffic is encrypted and authenticated.
- Role-based access control (RBAC) – defines which services can talk to each other.
- Certificate management – automatically issues and rotates service certificates.
Example in Azure:
Open Service Mesh integrates with Azure Key Vault for secure certificate management and Azure AD for service identity.
3. Observability
In distributed systems, identifying bottlenecks or failures is challenging. A service mesh provides deep observability through:
- Metrics (latency, error rate, request volume).
- Distributed tracing across microservices.
- Logging for auditing and debugging.
Example in Azure:
With OSM on AKS, observability integrates with Azure Monitor, Log Analytics, and Application Insights, providing full-stack visibility.
Best Practices for Service Mesh in Azure
- Start small, scale gradually – begin with a pilot project before applying a service mesh across all workloads.
- Leverage managed integrations – use Azure-native tools like Key Vault, Monitor, and AAD for simplified operations.
- Balance complexity – Service Mesh brings powerful features but adds overhead. Only enable features (like tracing or strict mTLS) as required.
- Automate policy management – enforce security and traffic rules through CI/CD pipelines.
When to Use a Service Mesh
Adopt a service mesh in Azure if your application:
- Has many microservices with complex communication patterns.
- Requires strong service-to-service security and encryption.
- Needs end-to-end observability for debugging and performance optimization.
- Operates in multi-team or multi-cluster Kubernetes environments.
For simpler workloads, standard Kubernetes networking or Azure Application Gateway Ingress Controller (AGIC) might be sufficient.
The Service Mesh architecture pattern is a critical enabler for running scalable, secure, and observable microservices on Azure. By handling service-to-service communication, security, and observability, it allows developers to focus on innovation while platform teams manage cross-cutting operational concerns.
With Azure-native integration through Open Service Mesh (OSM) or other CNCF service meshes like Istio, enterprises can achieve zero-trust security, fine-grained traffic control, and rich observability—all while reducing the burden on development teams.
Adopting a service mesh in Azure is a strategic step toward building resilient, cloud-native applications that can thrive in today’s dynamic environments.